Authored by Jodi Fifer, CPA, CISA | Director & Ryan Nowicki | Manager
Auditors, often in collaboration with compliance tools, are racing to offer faster, lower-cost SOC 2 certifications. But recent controversies in the news revealed that some compliance platforms are cutting corners, leaving your business exposed to major risks. If you’re in the market for a SOC 2 auditor, here’s what you need to know before you sign anything.
The rise of SOC 2 audit mills (and what it means for you)
SOC 2 audits are designed to be thorough and doing them correctly takes time. But as they’ve become a US standard, businesses are looking for faster, cheaper ways to get certified. Certain audit firms, often called “audit mills,” have emerged to meet that demand, issuing SOC 2 reports with minimal attestation work and effectively “rubber-stamping” the results. If you think this sounds too good to be true, that’s because it is.
Just this week, a popular AI gateway startup, suffered a serious malware attack after receiving their SOC 2 certification from an audit mill. The breach exploited gaps in the exact controls SOC 2 is supposed to verify. The company has since dropped its compliance vendor and is starting over with a more traditional auditor.
A bad audit doesn’t just produce a worthless report. It leaves your systems exposed and your customers at risk.
The risks of choosing the fastest, cheapest SOC 2 auditor
While lower cost and faster timelines can be attractive, simply choosing an auditor based on these promises can come with real consequences.
False sense of security
On paper, your SOC 2 report may look well-documented. But if the audit process lacks real validation, depth, or clear boundaries or understanding of the system, gaps in your security may exist and go unnoticed, and your organization is left exposted – and you have no idea.
Real-world incidents like the Change Healthcare breach, which cost UnitedHealth an estimated $2.87 billion, is a reminder of what’s at stake when security controls exist on paper but fail in practice.
Lost deals and revenue
You’re close to closing a deal with a large customer. As part of their due diligence, they review your SOC 2 report. Something doesn’t add up – the report raises questions, and suddenly you’ve lost the deal.
This is a common story. Recent studies show that 57% of businesses have terminated a vendor relationship due to security concerns in the past 12 months.
Reputational damage
A weak or inconsistent SOC 2 report can signal to customers and partners that your organization may not take security seriously. If issues surface, that perception can be difficult to reverse and can impact trust across your business.
Having to redo the audit
Months after completing your SOC 2, questions start coming in. The report doesn’t hold up under scrutiny. Now you’ve found yourself starting over with a new auditor, sinking twice the time and cost into your audit – just like the story above.
Red flags: When a SOC 2 audit should raise questions
On the surface, many SOC 2 audits can appear credible. Here’s what to look out for:
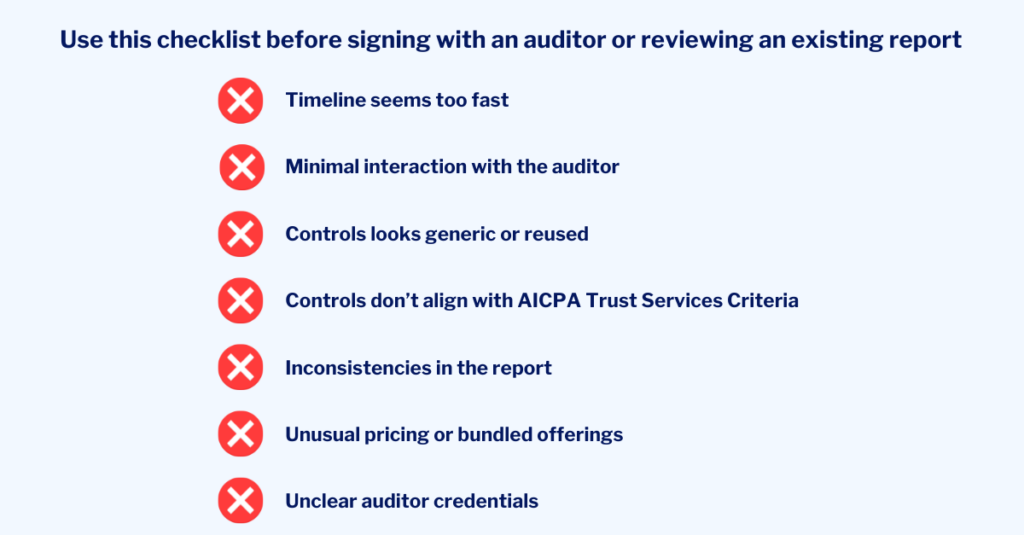
Spotting these red flags makes it easier to ensure you’re taking the right steps in protecting your organization.
How to choose a SOC 2 auditor & protect your organization
Whether you’re looking to receive a SOC 2 audit or reviewing an existing one, taking a closer look at the details can save your business’ reputation.
If you’re choosing an auditor:
- Ask what a typical timeline looks like and how the audit process is structured
- A legitimate SOC 2 audit typically requires a minimum 3-month observation period, with 6–12 months being the standard.
- Understand if the controls will be tailored to your environment, or templated by a platform
- Check if your auditor plans to validate controls, especially if they are coming from a compliance tool.
- Verify the firm’s credentials, peer review, and license status using AICPA’s database of credible auditors
- Check for an active peer review on record and confirm the firm is licensed in the state where they’re registered. If either is difficult to verify or the firm has a minimal U.S. presence, dig deeper.
- If vendors are carved out of scope, ensure they are appropriate and consistently documented throughout the report
- Vague or inconsistent carve-outs can leave significant gaps in your coverage.
If you already have a SOC 2 report:
- Compare the system description to the actual controls audited, as well as the testing results, and look for gaps or inconsistencies
- The system description should be specific to your organization, and all sections should align. If a control is described in one section but absent or untested in another, that’s worth flagging with your auditor or an independent reviewer.
- Make sure the scope and Trust Services Criteria align with what is actually being tested
- If your customers require Availability or Confidentiality and your report only covers Security, you may have coverage gaps that need to be addressed.
- Review the auditor’s opinion and supporting test procedures for clarity and completeness
- A qualified or adverse opinion should be taken seriously. Even an unqualified opinion deserves a closer look if the supporting evidence feels thin.
- Take time to validate the audit firm rather than assuming credibility
- Search the firm in the AICPA’s peer review database and confirm their CPA license is active in their registered state. If you used a compliance automation platform, independently verify that their auditors are legitimate.
A SOC 2 report is only as valuable as the work behind it. Make sure someone actually did the work. If you’re looking to select an auditor, change your current auditor, or want to take a closer look at your current report, now is the time to do so. Connect with us.





